Jack in, it’s cyber-time. Seriously though if you are still reading, I squeezed on the Rift $399 bundle with touch that went active last week. I want to describe the experience of moving through a virtual environment and seeing your hands map in that realm, as to in reality, but it’s really something you have to try to get full appreciation of. I’m going to overview the hours I spent in so far, using Oculus software, enabling SteamVR and also some games and titles.
2017-08-17 Edit:
I wanted to mention Oculus Tray Tool and setting Super Sampling. I have since upgraded my GPU to a 1080 Ti and am running Super Sampling @ 1.5. Oculus Tray Toll will also let you disable USB auto power save in one click and also give you access to Visual HUD Overlays / debugging options. The super sampling really cleans up the image quality to try and mitigate screen door effect / seeing pixels obviously.
/edit
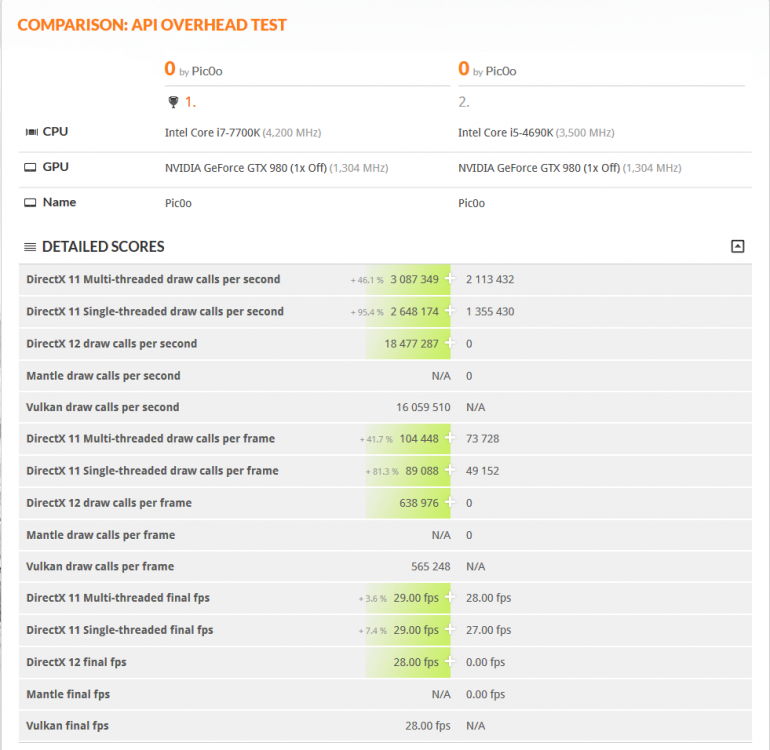
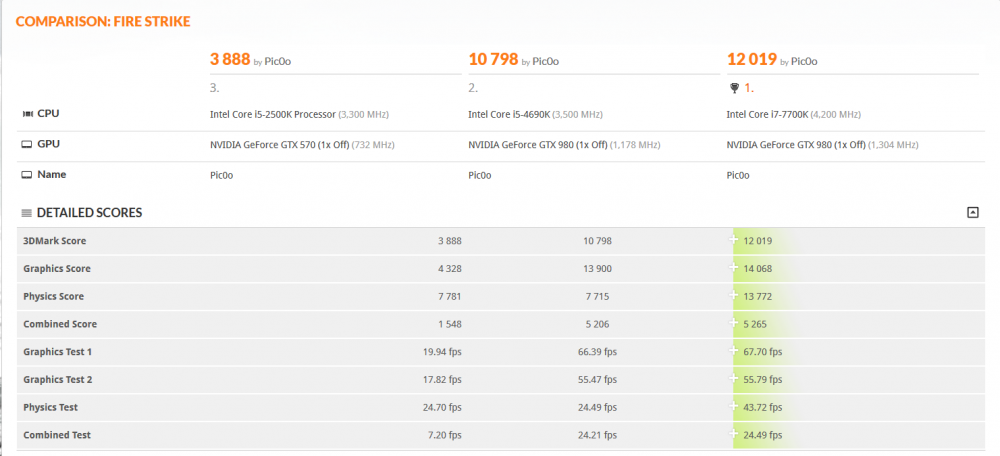
Primer here. You need a computer of comparable performance to drive the display of your Rift headset. I see a recommended spec of an Intel i5-45xx series processor / CPU and Nvidia 970 or higher for your video card / GPU. I recently built up an i7-7700k w/ 980 GTX build and it has performed extremely well in VR, without frame rate slowdown.
Your VR headset uses 1 HDMI and 1 USB connection, with the HDMI going directly into your video card. In my case, I already had my external display on DisplayPort. As the 980 GTX (and most recent cards from what I have seen) have 1 HDMI and the rest of ports are DisplayPort, you want to make sure your primary monitor is not using that HDMI output on the GPU / Video Card.
Additional hardware setup will be calibrating your spacial sensors, syncing any controllers and of course installing the Oculus software. Fair warning that Windows 8.1 seems to be the baseline and there are some games that require Windows 10. I’m on Windows 10 and wanted to warn you in advance, especially if you are still main-lining Windows 7. Most important of all, you need physical space to play the Rift.
There are a few sitting compatible games I have found, but the more explorational titles are going to need you to have at least a 3 x 3 foot area clear. From the center of your area, you will need to fully extend your arms to the side without being restricted. Movement depth is less relevant but also important. Some titles actually need you to be able to move back significantly far (as in around 7 feel away from the sensors). I have so far tested in a 3 x 3 area, as I would need to use the living room for the deeper dimensions. Since I picked up the Rift and Touch combo, I have 2 physical sensors installed. 1 came with the Oculus headset and the other came with the touch sensors.
I mentioned some of the contents but what you can expect to unbox are:
- 1x Oculus Rift headset
- 1x Sensor bar. It looks like a small camera. I suspect it works off Infrared similar to the Wii and Kinect devices.
- 1x Xbox One gamepad, USB dongle and extension cable.
- 1x Oculus remote.
- 2x AA batteries for the Xbox gamepad.
- 2x Oculus Touch controllers.
- 2x AA batteries. 1 for each Touch controller.
- 1x Oculus sensor
Once you clean up a space for you to move in VR without falling IRL, your first step after trying the tutorials (FYI: you can repeat these @ any time by clicking them in the desktop Oculus application, under your Library tab.), will be to get used to recalibrating center. This will be most appropriate when changing from standing or sitting play. In Steam you will get to the system menu by Right controller Menu button. There you will see a re-center calibration. If you are sitting, set your height to approx where your head is from the ground. I find 42 inches (3 ft 6 inches) works well for sitting. Some of this will need you to interact with Windows desktop for the height adjustment.
If you load SteamVR and are below the ground, you need to change your height settings.
Similarly in Oculus VR, the Right controller Menu button gives you a similar option to re-calibrate center. For height adjustment in Oculus, you’ll want to go to Settings | Devices | Configure Rift to change your height. You should be able to pick the re-center option without taking your VR goggles off, as with Steam as well.
Next post will cover some applications run in VR.
Most of these are on both the Steam Store and Oculus Store. I started in the Oculus store, until I was able to get SteamVR ruining. To get SteamVR to work you need to click the Gear icon for Settings on the desktop program, then click General. On this screen, enable the button for Unknown Sources. Once you do this, SteamVR will be able to interact with the Oculus gear, as before setting this option, Steam will say it cannot find your headset and accessories.
You will need to load SteamVR from your desktop, until or unless you enable the following mod to create a steam icon. In that guide, you are downloading a VR film, replacing the executable with a batch modified exe that loads SteamVR and also replacing some image files to show the tile in VR. Hack fun hacking up some custom icons with the info from that guide. It’s fairly easy to follow and you will then be able to launch SteamVR from within the Oculus VR environment.
I’m starting a little backwards describing my exploration but one of my main objectives was to interact with my desktop OS in VR. Steam handles this by selecting Desktop when you press the left menu button on a Touch pad. This will get you back to your actual (likely Windows) OS. I was browsing the twitter and reading email in VR. It’s a wild way to have a huge super desktop, while also letting you interact with VR games that launch from Desktop. Steam has a few of these but I have not encountered any in Oculus VR yet.
Kickass. Speaking of interacting with my desktop, I also wanted to try to see if I can open and manage files in a 3D realm. I can indeed open images, movies and music by using AVOlight.Space (Multi-Screen Media Player). The free download lets you load one screen and puts a watermark on each additional screen you load. This can be removed by buying the $9.99 DLC content to unlock the program. Seeing how it worked made it a no-question for me. This app has slideshow support, music and video controls, image rounding options along with depth perception to toggle zoom and placement of your displays. If you want to view some files in multiple windows, this is the jam.
Google Earth VR is a free download that allows you to browse Google Maps in 3D. If you ever switched visual modes and saw the tracking of depth for images, you will certainly see how the landscape is mapped as a rendered world with relative height and depth. This is pretty impressive to zoom and fly around in, granted I was moderate in controlling well the little I played in it. There are also area tours you can load up and enjoy, in the event you do not have any good ideas on where to search and visit. I wonder how restricted areas map. I’ll let you know on that one, since they are normally blurred out. Hopefully it doesn’t clip us out of the map. In this case, I was using the touch controllers as my primary input. Sitting compatible.
Lucky’s Tale. Included platformer game with some good level design. Graphics are cutesy like a Spiro-like game. You have height obstacles world maps that surround you. I was playing with the Touch controllers but this one appears to be designed for the gamepad / Xbox controller.
Oculus First Contact. This is likely the demo you play upon configuring your Rift. A very immersive interactive demo. I was mind blown in there and immediately suggested someone else try it too. Great demonstration and interactive guide on using Rift and Oculus. This is also listed in Tutorials as Touch Tutorial Complete.
Oculus Dream Deck. A video demo of a few oculus applications. Be sure to spin around and enjoy the world map, as the case with anything else you play.
Makebox. A slick pixel editor. I watched a video of someone giving a tutorial and was sold. I have to try and make some dank pixel art as well.
Darkness Rollercoaster. Sitting rollercoaster ride. Cool immersion and depth objects used.
Rick and Morty: Virtual Rick-ality. Very cool game that is a little difficult but rewarding. The VR design and implementation is quite good. You may find yourself restricted in a 3×3 foot space but can re-calibrate center to accommodate this. Crude humor and interesting use of environments. I have been playing this for a few hours and it is a standing title, as you are doing quite a bit of exploring and reaching down. I bought it on Steam, largely to test streaming functionality. I can say the streaming rooms do work in SteamVR. I finished this tonight in about 5 hours of playtime.
Be warned this game is designed for a Roomscale setup. That being a deeper area to walk around in.
Oculus Medium. Very robust image editing and world tool. You can save and export materials. Fun object creation and manipulation or a clay-like substance.
Mission ISS. This is a VR space simulator. You can pivot around the spaceship and enjoy the view.
Blocks by Google. Another image editor in a 3D space. Easel is your right hand where your drawing tool is the left one.
Preta: Vendetta Vising. This is a dungeon crawler game with multiplayer either coming or available after you complete the chapter 1 missions. I have an hour or two into this game. There are 3 character classes to pick from at start and some tutorials that keep you in a level environment. I was reserved on the quality of until I got to see some of the actual dungeons. The level design layering and depth is pretty impressive. Town is pretty close to most MMO-like RPGs. Quest NPC in Town, Skill up trainer, shops, etc. You get a bonus for early pre-release stuff but there is also a RMT item system. That’s a flag for performance down the line on growth. In other words, it may get very grindy of a game to encourage buying into currency boosts.
Sketchbox. VR prototyping platform. Really cool for prototyping a 3D environment. I’m going to try and import some 3D videos and do a mock-up environment. Especially if you want to make a VR application, mock it up in here on the swift.
EVE: Valkyrie . This is a flying space game. The controls seemed tight but it was fun for a space shooter.
Sports Bar VR. Standing game that I played last night. Darts, Air Hockey and Pool are available. I only played single player but it does feature online and lobbies.
The Climb. Standing game that I played about 2 minutes of due to sitting at the time of night when I tried it.
I will add more info about the last 2 games when I play them in a standing mode. This is what I got to explore so far. Some content is free and steam also appears to have some demos on there, I purchased the following or got them in a sale promo:
- Rick and Morty: Virtual Rick-ality: $30
- AVOlight.Space. Free single display. Unlock multiple for $10
- EVE: Valkyrie. Free with Summer of Rift Promo. Typically $40
- Makebox. $10
- Preta: Vendetta Rising. $35
- Darkness Rollercoaster. $2
- Oculus Adventure Pack: Includes for $70
The Climb
Raw Data
SportsBar VR
I Expect You To Die - Lucky’s Tale. Included with your Rift purchase.I also decided to pickup a 3rd sensor for better tracking when playing roomscale games. This is especially relevant when turning around and away from your desktop / front sensors. Adding the 3rd sensor will wrap you completely in motion tracking. I saw this when playing Rick and Morty and mitigated it using the recalibrate center steam menu option (that also is in the Rift menu).
I forgot to mention I got the $399 bundle by going to a Best Buy store and getting the Rift and Touch packages. When rung up at the register, it will be at the Promo rate and you’ll get the Oculus store coupon for your free copy of EVE: Valkyrie on the receipt. I have heard and seen that Amazon is pending more inventory, so head to a store and grab a kit if you don’t want to wait. Make sure they actually have ’em in stock, as I got the next-to-last headset last Saturday at a local store.
I did not see anywhere with the stand-alone sensors in stock so I ordered one from Amazon. They are also out of stock with no indicated restock date. I’m looking forward to setting up roomscale with 3 sensors to cover me when I turn around.
I have about 20 hours in VR so far and I am really enjoying it. I have been scouring the app stores for interesting free apps to check out too. Plenty of movies and some games to be found. Largely you have Oculus store, SteamVR store. Also a good resource is the Oculus Reddit page.
If you turn on Spectator mode in Rick and Morty but forget how to disable it, you need to do it from the in-game menu. Open the entertainment center right cabinet and toggle the switch. :)These are items included with your equipment purchase. EVE being an add-in for the Summer promo.
- Lucky’s Tale
- Medium
- Toybox
- Quill
- Dead and Buried
- Dragon Front
- Robo Recall
- Eve: Valkyrie
There are some good threads for applications and games on the Oculus forums. Medium has some real quality artwork and posts in there to explore. Lots of artwork to enjoy in this thread.
I turned off the tracking grid shortly after getting used to how much physical gaming space I had. Seeing the block grid was wrecking my immersion. You can turn off the floor grid indicator as well. You can do these in Oculus VR from the right touch controller settings menu. I’m guessing this is what people mean by ‘screen door effect’?
I should have a 3rd sensor hooked up early next week. 2 should be fine for most everything, but if you are playing a roomscale heavy game like Rick and Morty. I’ll be following this Oculus guide for configuring and placing sensors for roomscale. Edit with 3 sensors hooked up. It will have you re-run the configuration wizard and welcome tutorial when the 3rd sensor is plugged in. You really want all 3 of these sensors at the same level height. Otherwise your FOV will be highly skewed to the highest sensor.
Recalibrate your height to confirm your standing height (or change it to your head from ground while sitting (42 inches / 3 foot 6 inches in my case)). The avatar editor has a background with a ruler, if you take a selfie from the customize screen.
To change your standing or sitting height, in the Oculus desktop software, click the Gear | Settings. Along the left you will see Devices | Configure Rift | Floor Position. If you are playing a sitting or gamepad game, this may be helpful it adjust your field of vision.Respect to the Overclockers.com.au community for tipping me off to running Oculus Tray Tool. ASW mode will help with performance and you can also disable power-saving for the usb ports to keep your tracking active while playing. There are some Virtual HUD overlays that are helpful for debugging and performance monitoring.
Also of note from the forums is that switching to the Beta version of Oculus Home, it will detect your SteamVR titles on launch and add them into the Oculus app. So you don’t have to side-hack an icon for SteamVR using this method. Once you load the Steam title, it will pop into your Oculus applications menu.
Your headset has a microphone and it is on by default. If you wish to disable this as I did, jump into your Control Panel | Sound. In your list of Recording devices, right-click on the Rift Audio microphone and select Disable. If you want to turn it back on, be sure to check the ‘Show disabled devices‘ option so you can see the microphone to re-enable it.
Speaking of Steam, The Lab is a 15GB or so VR platform you can give a try to. I played around with it briefly in the lab and some of the other mini-games. Pause to note your standing height absolutely matters for this, so if you have your Room Config in steam set to a sitting height, you need to change that to your standing height. This varies from game to game, but is especially dominant on steam from when going from a standing to sitting game. Oculus seems to better accommodate sitting or standing, without needing to re-adjust your height, but by using the ‘reset app position’ from the main oculus home menu.
Stand-out applications have to be Google Earth VR. It’s really wild to see the area topography and be able to fly around in spectator-like mode around the world.
Dactyl Nightmare has been re-made into Polygon Nightmare. This is a re-creation that is pretty wild and fun as a single-player bot deathmatch. You may get ill from the movement, but I played for about 40 frags, enjoying the strafing with my upper body to move around the map. Both Google Earth VR and Dactyl Nightmare are free apps.
I have put some hours into Chronos as well. It’s a good exploration / puzzle game that keeps me drawn in. The leveling mechanic is interesting and has me getting a little angry when I die for sloppy reasons. The level exploration is really rewarding in 3D. Worth the $40 if you ask me.In respect to demo’ing VR, people really need to wear the headset. If you watch the on LCD output, it will be super bland without the depth. I had my GF try a few things and so far the immersion hit hard with Google Earth VR. She was off exploring the world, juggling views and continents.
I have also dabbled in Rock Band VR as a local store had one of the Xbox One guitars in the back. Apparently those things are going for $90 on Amazon, despite being $40 new if you can find one in stock. I did chuckle at having to flash the guitar firmware for it to work with RB VR. It did indeed work and when playing, I was reminded that I am not a rhythmic person. I only got an hour or two into that game so far. Considering the price of game ($50) and the Guitar ($40 with Xbox One Rivals Rock Band pack), this is a more costly game to get into. I have to say the use of the touch and the add-on mount that came with your controllers, is pretty cool with showing the Guitar on your person in VR and the crowd around you.
Darknet is a puzzle game about hacking computer networks. It uses a cluster honeycomb design where you pick insertion points for various vulnerabilities to spread to nodes, allowing you to seize the network and obtain root. Really cool graphical design and addictive gameplay. A good score for the $10 asking price.
Thanks for the feedback on your time with it. I wear glasses of 1.25 or so prescription so that may play a factor in my not being as bothered by the pixelation. I don’t wear my glasses in VR. Glad to hear you were able to work a refund out too.
I saw some people are bumping up the image quality using super sampling (via Oculus Tray Tool), similar to playing FFXI with better looking textures. A few of the VR games I played have some native graphic options, namely Chronos. Bumping up that IQ makes a huge difference, as the default in that is definitely a pixel show when you get close to your character.
I forgot to mention you are right about the length of games for VR. Many of them seem to be a few hours. Hopefully the surge of headsets gets more content out there. I think a big part of the challenge will be quality to performance cost, as top-end video cards and most other PC components to go with the headset, will make the barrier of entry even higher.
2017-08-04 edit:
I installed these sensor wall mounts in my play area and the floor and 360 coverage is MUCH better than when I had them on the included posts at desk height. The linked 3D print, I had to file the diameter wider for the IR camera to fit in, but other than that it works great. I used the double-sided tape mounts from 3M, as to not wreck the drywall in my apartment.
Sensors are mounted roughly 6.5 ft from the floor, aiming downward. This helped full 360 rotation and ground coverage quite well. My crude diagram of camera placement is:
_______________________
| <- 02 <- 01 |
| |
| |
| |
|<- Sensor 03 |
_______________________Sensor 01 is along the wall where my desk is in the corner.
Sensor 02 is about 5 feet away from the corner sensor.
Sensor 03 is about 10 feet from the back wall where 01 and 02 are installed and about 6 feet from sensor 2 to the corner of the adjoining wall.
I have the front 2 sensors lightly at inward angles to the area I stand, with sensor 3 pointing, basically back to my monitor between sensor 01 and 02. This also passed my Rick and Morty floor grab test, vastly better than the prior desk height mounts.I just received my prescription WIDMOvr lenses last night and have been playing every other night on average. The glasses insert is excellent. Great quality lenses that match my glasses prescription, the frame insert fits well into the stock Rift face guard and the elastic for the rift cover also helps keep the lenses in place. There is room between the rift lenses and the inserted prescription so you do not have to worry about scratching. I tried using the rift with my normal glasses but did not go that route because of tight removal and scratch threat. I can still see but my clarity is better with my prescription, for point of reference.
I also picked up a 3 ft usb and hdmi extension cables. The HDMi cable is an Insignia brand extension from a local BestBuy, that I found in the television section. I went with an Amazon basics 3 foot usb3 extension as many people referenced it for working well. I had some issues getting audio to play consistently over the extensions on my desktop, but then I added an Inateck Superspeed 4 Ports PCI-E to USB 3.0 Expansion Card as I saw some Oculus folks on reddit talk about the sensors and headset eating up much of the USB bus bandwidth. I do have to say, my extension issue went away installing this card and putting 2 of my 3 sensors on it, with the Rift HMD hooked to the USB on my motherboard.
Besides hardware I have been playing some games. Also a fun program is Bigscreen. It’s comparable to Desktop mode when running Steam but I think it has better touch button binds. I find it very nice for interacting with my desktop windows, while still in VR. Right-click, Left-click, mouse cursor and scrolling are all done on either hand. You can hat-press to remove the login screen when you load the program up.
Face Your Fears is a free program that has 2 doors to cinematic experiences. The city door is pretty intense, while the haunted house door… is pretty damn freaky. I was suggested to check this out by a friend and we were both scared af by the haunted house. Lol, you might not want to let kids try this one, because it’s damn creepy or I’m just a pansy. :p Sitting or standing experience, granted you are really just spectating and adjusting your head to view the area you are in.
Batman Arkham VR gets review beef for being a short experience, but take note is is also a great one. The quality of graphics, tools and interaction is top notch. If you want to see a viable peek into what a full VR game done with high production value looks like, this is one to buy. It has replay content for re-doing the story and I was well embracing the story it presented and some of the easter egg content. It’s $20 but looking at the extent of the content, I feel it is worth the asking price. If you enjoyed previous RockSteady Batman titles, this will show you the new shit coming down the pipes. This supports sitting and standing play, but lends better to standing play.
Technolust: Extended Format is a game you can blast through but you will certainly miss most of the relevant story and not have explored the world or options. I got 20+ hours out of this easily. It has mini-games too, but the interactions and narrative that go with the in-world are what are to be best enjoyed. This is an older game (haha so that means 2016 in VR terms) that has touch support added. Most of your aiming is actually done with your head instead of the gamepad / touch controllers. I’m on board with any more content released by this team. Easily one of my best purchases. Works well for sitting or standing exploration.
Windlands is something I saw mentioned as a game to try. It also has a ‘Buy it on steam and you will get an Oculus key’ feature through their website. I want to pause and say between the 2 stores, if you have an oculus, play the Oculus store version. The controller config is more likely to be optimized for that platform, as is the case with Wildlands on Steam being configured for a Vive and the Oculus Home version being configured for touch. There is an option for some games on Steam to ‘launch in home mode’, but this is not the current standard.
Back to this game, it is an exploration via grappling hook traversal. The areas are well done to have you figure out what route currently looks viable and how you are going to use your grappling hooks and jumping to obtain the objects on the world map. Very solid and good looking game. Plenty of control options between sitting and standing play.Nature Treks VR is a collection of area environments. Woods, underwater and other outdoor areas. This experience is pretty demanding on your computer, since it renders the entire stage area and surrounding creatures. Looks very cool to relax in and explore. You can use locomotion or teleport transportation. You can plant extra trees and stuff too.
Serious Sam: The Last Hope is a stationary shooter. If you played the other games, the enemies and stages will look familiar. Main take-away being you stay in place and shoot away hordes of monsters until you get to the world boss fight.
Rez: Infinite is a VR shooter with music note and scoring to your attacks. It’s a fairly short adventure but it’s done well and has some extra modes as well. The presentation and levels to boss fights are done well. $20 for this game. Both standing and sitting supported, as you move by controller and look by head rotation.
Mountain Goat Mountain is a free game that is simple but fun. Kind of like a Q-bert game to traverse the map, eat food and score coins.
I’m looking forward to jumping into some more VR stuff this weekend. I played a little more Preta: Vendetta Rising after they dropped the price and removed some of the RMT content. I am currently on mission 5 on chapter 1 but I’m not riveted by it so far.
I picked up a puzzle game called Dimensional for $5. One can only play so many gun shooters, both regular and VR wise. I am also going to try out Karnage Chronicles this weekend. It sounds like an impressive hack-n-slash game. I grabbed it on Steam, since it’s not yet on the Oculus store. checking the steam forums, it should detect and work with the oculus fine / find the controllers as touch instead of the vive wands.Nov 14th:
I took a break from VR, largely due to playing Nintendo Switch games. I also played Karnage Chronicles and got really VR sick, like terrible headaches and all. I know some people claim to be immune to vr / motion sickness, but wow, hacking and slashing in a dungeon wrecked me with locomotion controls.I visited my friend and his kids a few weeks ago and did a VR demo. They loved it, especially the older teen, as he is a huge pc gamer. I’m going to hook my gear back up this week and jump back in. I still have some ideas I want to try for creating some content, but in the mean time I’m also excited to try Obduction, from the Myst creator team. I also started Edge of Nowhere and should continue that tomb raider-like platformer.
Windlands is actually pretty fun but I got stuck within maybe an hour. Short of the issue of knowing where to proceed, it is quite fun grappling around the world map.I may pickup Doom VFR but I want to see how it is received and if it gets actual oculus support. I’m thinking I’ll pickup Skyrim again but on the Switch, since it’s a huge game and being able to play it in tablet mode will make it more accessible over time. According to steam, I dropped 202 hours on the PC edition (Level 37 and surely some idle time with the game running). It looks like I played the Dawnguard expansion too.
Jumping back to VR, I played .Hack in BigScreen. Wild with the giant screen and the map being in the top right of my full view pane.
If you recently have terrible tracking jank or lag with your head movement tracking, may I suggest updating nvidia drivers. Especially 388.13 in my case. I do note that I had a 3D vision driver installed as well, that I removed before upgrading to 388.31 edition drivers.
Since I do not use the 3D capabilities I try to uncheck the install via Custom Installation. I’m not a user of Nvidia Experience either and manually put new ones (drivers) in fairly often. I was going raw on troubleshooting by switching cables and distributing across USB controllers, but the driver conditions above fixed me back up.
My issue was especially visible on the Oculus home menu. My tracking sensor locations were similar to prior sessions this week. I was happy to weed it down to a driver factor after a little ghost hunting on the troubleshooting.
If you think Windows 10 is noisy, you should enjoy the connections your PC will make to graph.oculus.com. I Blacklisted that for a few minutes to notice none of the store content displayed. I could still view and load my library though.